For the second year in a row, Carnegie Mellon’s competitive hacking team, the Plaid Parliament of Pwning(opens in new window) (PPP), has taken home the top prize at the MITRE Embedded Capture-the-Flag (eCTF) cybersecurity competition(opens in new window).
Over the course of three months, PPP, and 79 other collegiate-level teams, worked to design and implement a key fob system for a car door lock, protecting the car from unauthorized entry and preventing attacks such as replays and key fob cloning.
PPP’s win came in a landslide, scoring over 10,000 more points than the competition’s second-place finisher. CyLab Security and Privacy Institute Project Scientist Maverick Woo, who co-advised the team with Electrical and Computer Engineering (ECE) Professor Anthony Rowe and Information Networking Institute (INI) Associate Teaching Professor Patrick Tague, credited the victory to the group’s composition and work ethic.
“Our team has strong expertise in both embedded development and attacks,” said Woo. “Our students worked hard and were committed, and they were able to organize themselves to take advantage of the large team size.”
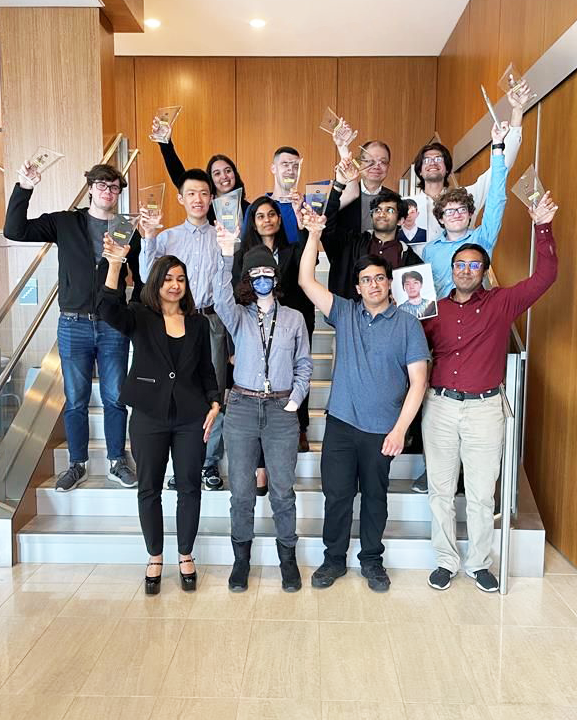
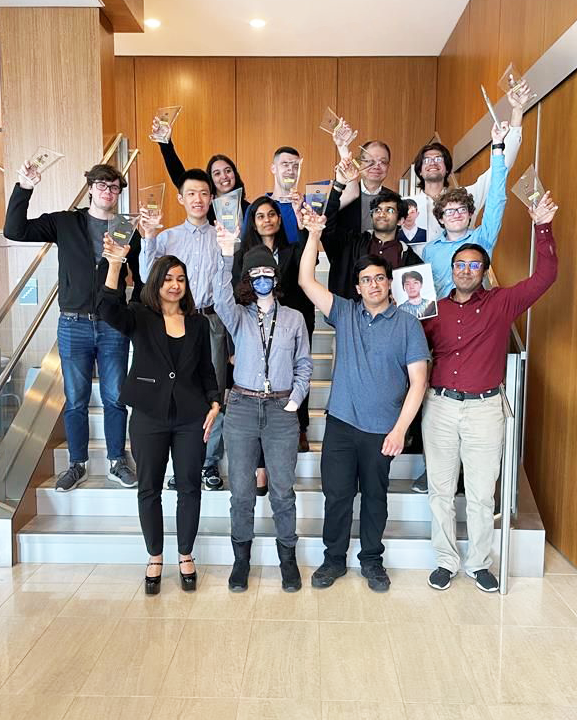
The annual competition saw teams from the United States and around the world, with a record-breaking 546 student participants. Notably, PPP finished ahead of hackers from the University of California, Santa Cruz (2nd place), and the University of Illinois Urbana-Champaign (3rd place).
The competition had two phases — design and attack. Each phase offered opportunities to score points by obtaining flags and submitting them to the live eCTF scoreboard.
During the design phase, hackers acted as a team of engineers at a car manufacturer, designing and building the embedded software that would get provisioned on the next line of cars and key fobs sold to customers. In the attack phase, teams had the opportunity to analyze other groups’ designs, identifying security flaws as they aimed to unlock and start the vehicles without authorization from the vehicle owners.
eCTF competitions are unique from other CTF competitions because they focus on embedded systems security. Students not only defend against traditional cybersecurity attack vectors but also need to consider hardware-based attacks such as side-channel attacks, fault injection attacks and hardware modification attacks.
“These competitions offer students a unique opportunity to combine the knowledge and skill sets obtained in various cybersecurity, computer science and computer engineering classes and apply them to real-world situations,” said INI Assistant Teaching Professor Hanan Hibshi. “Over the years, former students have shared how these experiences impacted their careers and their understanding of the concepts we discuss in class.”
“Before competing in eCTFs, I had almost no security experience. Thanks to competitions like this, I now understand the basics of cryptosystems and have gained hands-on experience performing attacks and designing secure systems,” said Carson Swoveland, a junior in ECE.
“This competition was a fantastic opportunity to apply hardware attacks I had only read about in practice,” says ECE master’s student Eliana Cohen. “I learned a ton, and I’m excited to apply my experience as I begin my career.”
Funding for this year’s team was made possible by several current and former CyLab Security and Privacy Institute partners: Amazon Web Services, AT&T, Cisco, Infineon, Nokia Bell Labs, Rolls Royce and Siemens.